Ssh Keygen Mac For Root Login
• ssh-copy-id demo@ 198.51.100.0 Note: If you are a Mac user, ssh-copy-id will not be installed on your machine. Family tree chart. You can, however, install it using: • brew install ssh-copy-id Alternatively, you can paste in the keys using SSH: • cat ~/.ssh/id_rsa.pub ssh demo@ 198.51.100.0 'mkdir -p ~/.ssh && chmod 700 ~/.ssh && cat >> ~/.ssh/authorized_keys' No matter which command you chose, you may see something like: The authenticity of host '198.51.100.0 (198.51.100.0)' can't be established.
Don't use a password. Generate a passphraseless SSH key and push it to your VM. If you already have an SSH key, you can skip this step Just hit Enter for the key and both passphrases: $ ssh-keygen -t rsa -b 2048 Generating public/private rsa key pair. Jul 13, 2012 Mac OS X (10.7.4) Posted on Jul 3, 2012 6:21 PM. Reply I have this question. It is possible to give the root account ssh-keygen keys and ssh into the root account WITHOUT needing to enable the root account's password. Rsync as root needs ssh root login. How To Set Up SSH Keys Posted June 22, 2012 4.1m views Linux Basics Security. Ssh-keygen -t rsa Step Two—Store the Keys and Passphrase. Optional Step Four—Disable the Password for Root Login. Once you have copied your SSH keys onto your server and ensured that you can log in with the SSH keys alone. Second, I highly suggest you continue to login as root with a key with a password. If you do not want to enter a password every time, add it to ssh agent. On the command line this would be ssh-add ~/.ssh/key_name.
Written by Date: 2013-01-24 22:40:13 00:00 SSH keys Log into ssh servers (Mac OS X or Linux) without passwords, using ssh key. How to generate them with ssh-keygen and install on the server — Arch Linux Wiki Generate ssh keys To generate your private and public keys for ssh login with no password we will use ssh-keygen in the client computer (The one that will log into the server using ssh) ssh-keygen -t rsa It will ask you for a passphrase, is up to you to use one or not. Here are the pros and cons. Pros • Extra security • If you lose your private key, no one will be able to use it.
Once the key has been authorized for SSH, it grants access to the server without a password. Use a command like the following to copy SSH key: Enter the following command to copy your public key to your Node: ssh-copy-id user@xxx.xx.xx.xx This will copy your public key to the authorized_keys file on your server.
Note: it can be multiple keys and adding extra authorized keys can easily happen accidentally! If ssh-add -L returns no keys, then the most recently modified key matching ~/.ssh/id*.pub, excluding those matching ~/.ssh/*-cert.pub, will be used. -n Just print the key(s) that would be installed, without actually installing them. Unistall tool avg for mac. -o ssh_option Pass -o ssh_option to the SSH client when making the connection.
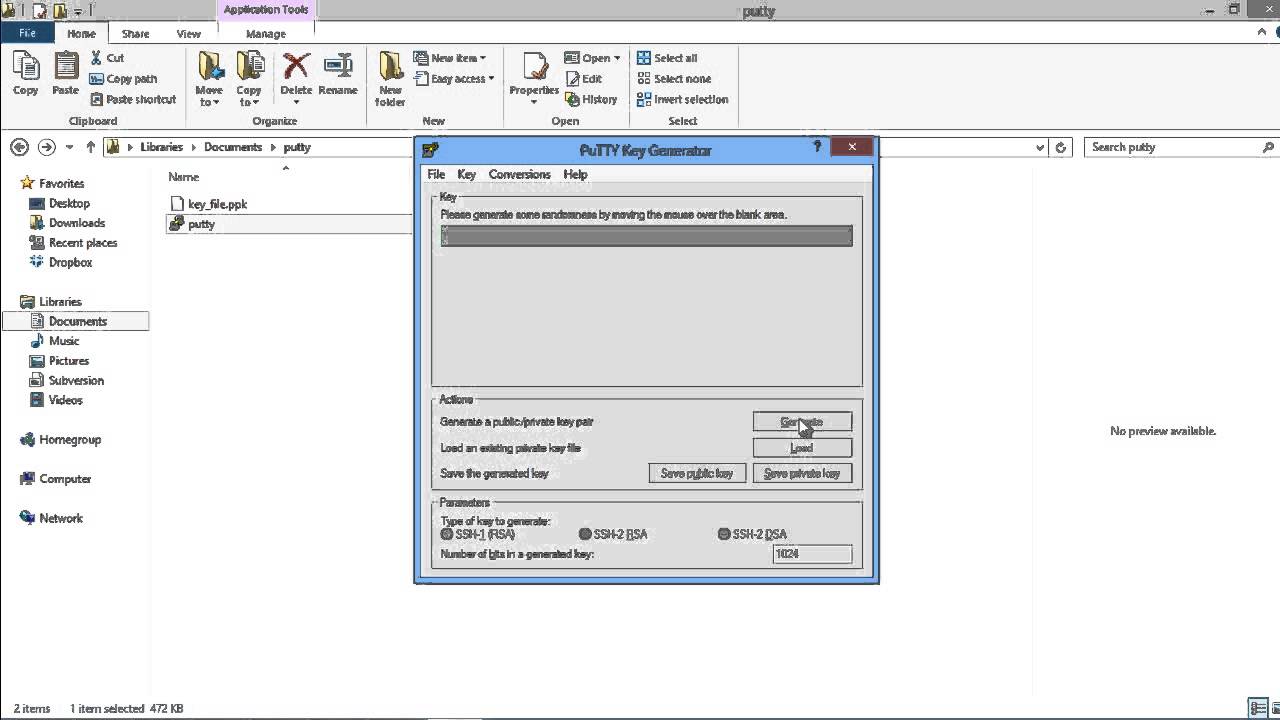
You can test to make sure you got everything correct at this point by doing the following command: sudo apt update You will be promopted for your password and then should see the package list update. If you get a permission denied after doing the password correctly, make sure you have executed sudo usermod -aG sudo hoban, replacing hoban with whatever user you created. You will need to do this as root, and relogin as your user when adding a group. Create SSH Key At this point, we want to create our SSH key pair, this is a public and private key you will use as a what you have type of security. Using a passphrase on your key is optional, but I highly recommend using a passphrase. Once you use an SSH key for authentication, that is all that is required to get into any server you add your key to. Torrent for mac 2015. Without a passphrase, they don't need to know anything, they only need access to your private key.